NEWSLETTER - Q4'25 - Q1'26 - Industrial Cyber Threats
NEWSLETTER
Industrial Cyber Threats
Period: Q4'25 - Q1'26
#icscybersecurity #otcybersecurity #industrialcybersecurity

The release of the latest report from Dragos provides one of the most comprehensive looks at the evolving cyber threat landscape targeting operational technology and industrial control systems.
The 2026 OT ICS Cybersecurity Year in Review examines adversary activity observed throughout 2025 and highlights a critical shift in how attackers approach industrial environments.
For many years, security professionals viewed cyber threats to operational technology primarily as reconnaissance or intelligence gathering operations. Attackers would gain access to industrial networks but often stopped short of manipulating physical processes.
That is no longer the case.
The report shows that adversaries are increasingly studying industrial processes themselves and mapping how systems interact to enable real-world operational disruption. (dragos.com)
This evolution represents a fundamental change in industrial cybersecurity risk. The threat is no longer limited to data theft or network intrusion. The focus is shifting toward physical operational impact.
Understanding this shift is critical for organizations responsible for protecting energy infrastructure, manufacturing facilities, transportation systems, and other industrial environments.
The Industrial Threat Landscape Is Expanding
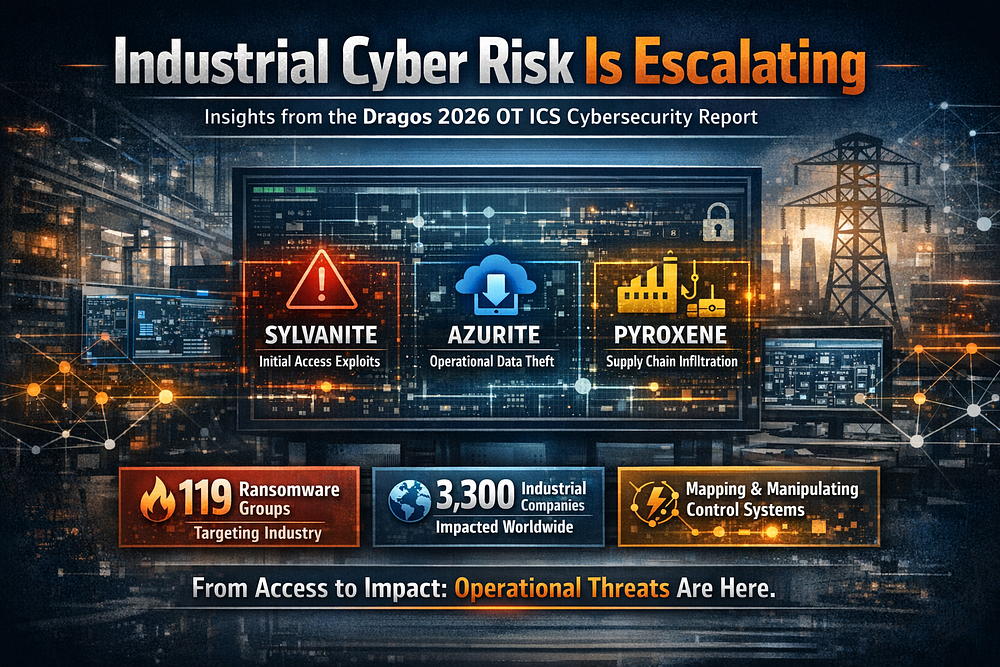
One of the most significant findings in the report is the emergence of three newly tracked advanced threat groups targeting operational technology environments.
These groups illustrate the increasing specialization of industrial cyber adversaries.
This shift toward specialization mirrors the evolution previously seen in enterprise cybercrime ecosystems. Different actors increasingly handle different stages of the attack chain initial access, intelligence gathering, operational disruption, and monetization. The appearance of specialized roles within industrial threat activity suggests the ecosystem targeting operational technology is maturing rapidly
SYLVANITE
SYLVANITE operates primarily as an initial access broker within the industrial threat ecosystem.
Rather than conducting full attacks independently, this group focuses on identifying and exploiting publicly facing vulnerabilities in infrastructure systems. Once access is obtained, it is often handed off to other threat actors who perform deeper operations within the environment.
This model mirrors patterns already seen in enterprise cybercrime ecosystems where specialized actors handle different stages of the attack chain.
For industrial environments, this development is particularly concerning because it means attackers are building supply chains of compromise.
Initial access may be gained quickly through exposed gateways, remote access systems, or poorly secured services.
Once inside, other actors can move deeper into operational networks.
AZURITE
AZURITE represents a different type of industrial adversary.
Rather than immediately attempting disruption, this group focuses on long-term operational intelligence gathering.
Investigations revealed that AZURITE conducts interactive operations on engineering workstations and other control systems to extract sensitive operational data.
This includes information such as
Process configurations
Control logic
Network architecture
Operational documentation
The purpose of this activity appears to be preparation for future operations rather than immediate sabotage.
By collecting detailed knowledge of industrial processes, attackers can later design operations that manipulate physical systems with far greater precision.
Researchers observed that the group demonstrates awareness of industrial software environments and engineering workflows, indicating growing expertise among adversaries targeting operational technology.
PYROXENE
The third newly tracked group, PYROXENE, demonstrates a different tactic that reflects the expanding attack surface of modern industrial environments.
Rather than relying solely on technical exploits, this group leverages supply chain compromise and social engineering techniques.
This includes activities such as
Compromising trusted vendors
Impersonating service providers
Manipulating human operators or administrators
These tactics allow attackers to bridge the gap between enterprise IT systems and operational technology networks.
The use of social engineering and supply chain attacks highlights a key reality in industrial cybersecurity.Technical defenses alone are no longer sufficient.
Human trust relationships and vendor ecosystems have become major pathways for compromise.
A Growing Ecosystem Of Industrial Threat Actors
The addition of these three groups brings the total number of tracked industrial threat groups to twenty six globally, with eleven actively conducting operations during 2025.
This expansion reflects what researchers describe as the maturation of the industrial cyber threat ecosystem.
Industrial control systems are now viewed by adversaries as high value strategic targets.
Critical infrastructure provides leverage. Manufacturing downtime causes immediate economic damage. Energy disruption can create political instability.
As a result, threat actors are investing more time and resources into understanding how industrial systems operate.
Attackers Are Learning How Physical Systems Work
One of the most concerning observations in the report is the increasing amount of effort adversaries are putting into studying industrial processes themselves.
Historically many attackers treated operational technology access as simply another foothold inside a network.
Today, the situation is very different.
Researchers observed adversaries performing control loop mapping inside compromised environments. This involves systematically identifying the components that interact to control a physical process.
Examples include
Human machine interfaces
Variable frequency drives
Metering modules
Industrial gateways
By mapping how these components interact, attackers can identify where manipulating one system will cause cascading effects elsewhere in the process.
This level of analysis suggests that attackers are attempting to understand how to induce physical impact intentionally rather than accidentally.
Industrial systems are designed to control real world processes such as power generation, manufacturing, water treatment, and chemical production.
Manipulating those processes can lead to severe operational consequences.
The Dragos report notes that adversaries are now spending more time studying how physical processes behave and less time simply establishing passive access inside networks.
Evidence Of Operational Targeting Is Increasing
Another key finding is that operational targeting is no longer theoretical.
Real-world incidents observed in recent years demonstrate that attackers are willing to attempt disruptive actions against industrial infrastructure.
Researchers documented attempts targeting distributed energy resources and power infrastructure across multiple regions including Europe and the United States.
These incidents highlight an important reality.
Industrial cyber operations are increasingly tied to geopolitical conflicts and strategic competition between nations.
Energy systems, transportation infrastructure, and manufacturing facilities are all potential targets during times of political tension.
This trend means that industrial cybersecurity is no longer just an operational concern for individual companies.
It is rapidly becoming a national security issue.
Ransomware Continues To Impact Industrial Operations
While nation-state activity receives much attention, ransomware remains one of the most significant threats facing industrial organizations.
According to the report, ransomware targeting industrial environments increased dramatically during 2025.
Researchers tracked one hundred nineteen ransomware groups targeting industrial organizations, up significantly from the previous year.
More than three thousand three hundred organizations worldwide were affected by these campaigns.
Manufacturing remained the most heavily impacted sector due to its reliance on continuous production and tight supply chains.
For attackers, manufacturing downtime creates immediate pressure to pay ransoms.
Another important observation from the report involves dwell time.
The average dwell time for ransomware inside industrial environments was approximately forty two days.
This means attackers often remain inside networks for more than a month before triggering disruptive actions.
That extended presence allows them to
Escalate privileges
Move laterally across networks
Identify high-value systems
Prepare coordinated attacks
In many cases, attackers also attempt to disable backup systems and recovery mechanisms before launching ransomware.
Many OT Incidents Are Misclassified As IT Breaches
A recurring challenge in industrial cybersecurity is that many incidents affecting operational technology are incorrectly categorized as standard enterprise cyber attacks.
This happens because many OT assets run general purpose operating systems such as Windows.
When ransomware infects these systems the incident may appear to be an IT problem.
In reality, the operational impact can be far more severe. Engineering workstations often control production processes. Human-machine interfaces provide visibility into plant operations.
Compromising these systems can disrupt manufacturing lines, energy production, or safety controls. This misclassification can lead to underestimating the severity of incidents affecting industrial environments.
Industrial Threat Activity Is Global
Threat activity observed in the report spans multiple regions and industries.
SYLVANITE campaigns have targeted organizations in
North America
Europe
The United Kingdom
Asia
The Middle East
Industries affected include
Energy
Water utilities
Oil and gas
Manufacturing
Government infrastructure
AZURITE operations also span multiple continents and focus heavily on exfiltration of operational data.
Meanwhile, PYROXENE demonstrates the growing role of supply chain compromise and human-targeted attacks within industrial environments.
Taken together, these patterns show that industrial cyber threats are global and cross-sectoral.
No single industry or region can assume it is immune.
Visibility Remains The Most Important Defensive Advantage
Despite the concerning threat trends, the report also highlights some encouraging defensive insights.
Organizations that had comprehensive visibility into their operational technology environments were able to detect and contain ransomware incidents far faster.
On average these organizations detected and contained incidents in about five days.
The broader industry average was forty two days.
This difference is significant. It demonstrates that improved visibility can dramatically reduce the operational impact of cyber incidents.
Visibility in this context includes
Comprehensive asset inventories
Monitoring of network communications
Awareness of remote access pathways
Understanding of industrial process dependencies
Without visibility, organizations cannot detect abnormal activity or respond quickly when systems are compromised.
New Technologies Are Creating Additional Blind Spots
Industrial environments are evolving rapidly as organizations adopt new technologies such as
Artificial intelligence driven automation
Battery energy storage systems
Distributed energy platforms
Industrial internet of things devices
While these technologies bring operational benefits they also introduce additional complexity into industrial networks.
Each new device or platform can create new pathways for attackers if it is not properly monitored and secured.
This expansion of the industrial attack surface makes visibility and architecture management even more critical.
The Strategic Lesson From The 2026 Report
The overarching message of the Dragos 2026 OT ICS Cybersecurity Report is clear.
Industrial cyber threats are becoming more capable, more specialized, and more focused on real-world operational impact.
Attackers are no longer satisfied with simply gaining access to networks.
They are studying how industrial processes work. They are mapping control loops. They are learning how physical systems interact. And in some cases, they are already attempting to disrupt those systems.
For defenders, the lesson is straightforward.
Industrial cybersecurity must move beyond traditional IT security thinking. Protecting operational technology requires understanding
Industrial processes
Operational risk
System architecture
Physical consequences of cyber events
Organizations that treat OT security as simply another IT problem will struggle to keep pace with adversaries who are increasingly focused on the physical world.


.png)
Comments
Post a Comment